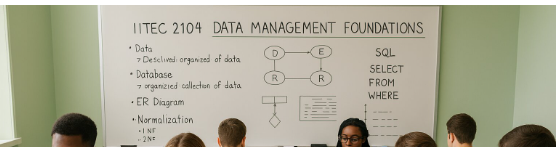
Data Management Foundations (C175 )
Access The Exact Questions for Data Management Foundations (C175 )
💯 100% Pass Rate guaranteed
🗓️ Unlock for 1 Month
Rated 4.8/5 from over 1000+ reviews
- Unlimited Exact Practice Test Questions
- Trusted By 200 Million Students and Professors
What’s Included:
- Unlock Actual Exam Questions and Answers for Data Management Foundations (C175 ) on monthly basis
- Well-structured questions covering all topics, accompanied by organized images.
- Learn from mistakes with detailed answer explanations.
- Easy To understand explanations for all students.

Free Data Management Foundations (C175 ) Questions
What is the practical significance of taking the logical view
-
False
-
Maybe
-
True
-
Not Sure
Explanation
Correct Answer C. True
Explanation
Taking the logical view in database design is practically significant as it allows the user to focus on data organization, relationships, and accessibility without worrying about the physical storage details. This abstraction helps streamline database design and ensures flexibility in adapting to business needs.
Why other options are wrong
A. False: It is incorrect to say that the logical view lacks practical significance, as it plays a critical role in organizing and structuring data effectively.
B. Maybe: This option does not provide a definitive answer. Logical views are definitely significant in database design.
D. Not Sure: This does not address the question directly. The logical view has clear and practical importance in database design and management.
A binary relationship is a relationship between two entity types
-
Cardinality
-
Binary relationship
-
Associative entity
-
Attribute
Explanation
Correct Answer B. Binary relationship
Explanation
A binary relationship is defined as a relationship between exactly two entities in the entity-relationship (ER) model. For instance, a relationship between the "Student" entity and the "Course" entity (e.g., "Enrolls In") is a binary relationship because it involves two entities. Binary relationships are the most common type of relationships in database design.
Why other options are wrong
A. Cardinality: Cardinality refers to the number of entities that participate in a relationship and specifies constraints, such as "one-to-many" or "many-to-many." It does not describe the nature of the relationship as being between two entities.
C. Associative entity: An associative entity is used to represent a relationship in cases where additional attributes are associated with the relationship itself. It is not the term for a direct relationship between two entities.
D. Attribute: An attribute is a property or characteristic of an entity, not the relationship between two entities.
Which notation easily identifies multivalued attributes according to the text
-
Foot
-
Chen
-
UML
-
Bachman
Explanation
Correct Answer B. Chen
Explanation
The Chen notation, commonly used in Entity-Relationship diagrams, easily identifies multivalued attributes by representing them with double ovals. This graphical representation distinguishes them from other types of attributes.
Why other options are wrong
A. Foot: Foot notation is not a commonly recognized method for identifying multivalued attributes.
C. UML: UML (Unified Modeling Language) is primarily used for object-oriented design and does not explicitly highlight multivalued attributes as clearly as Chen notation.
D. Bachman: Bachman notation focuses on relationships but does not emphasize multivalued attributes in the way Chen notation does.
What is a relationship defined as according to the text
-
Association between Entities only
-
Association between Objects only
-
Association between Objects, Entities, Databases, Fields
-
Association between Databases only
Explanation
Correct Answer A. Association between Entities only
Explanation
A relationship in database terminology refers to the association between two or more entities. This association helps define how entities interact with one another in a database model.
Why other options are wrong
B. Association between Objects only: Relationships in databases are not limited to objects but primarily focus on entities.
C. Association between Objects, Entities, Databases, Fields: This is an overly broad definition that includes concepts unrelated to the core database definition of a relationship.
D. Association between Databases only: Relationships are about the connections between entities, not databases themselves.
A derived attribute
-
Must be stored physically within the database
-
Need not be physically stored within the database
-
Has many values
-
Must be based on the value of three or more attributes
Explanation
Correct Answer B. Need not be physically stored within the database
Explanation
A derived attribute is an attribute whose value is calculated from other attributes. Since it can be generated at query time, it does not need to be stored physically within the database, reducing storage redundancy.
Why other options are wrong
A. Must be stored physically within the database.
Storing derived attributes physically in the database is unnecessary because they can be calculated dynamically. Doing so increases the risk of data redundancy and inconsistency if the derived value does not update with changes in base attributes.
C. Has many values"
Derived attributes typically have a single value derived from other attributes. The phrase "has many values" applies to multivalued attributes, not derived attributes.
D. Must be based on the value of three or more attributes
Derived attributes can be calculated from one or more attributes but are not required to depend on three or more attributes. The number of attributes involved depends on the specialculafic ction.
What are rows sometimes referred to as
-
Files
-
Fields
-
Records
-
Tables
Explanation
Correct Answer C. Records
Explanation
Rows in a database table are commonly referred to as records because they represent individual, structured data entries. Each row contains related information spread across multiple columns, such as all the details about a single entity like a student or product.
Why other options are wrong
A. Files: Rows are part of tables in a database, not standalone files. Files generally refer to units of data storage on a file system, which is different from database structures.
B. Fields: Fields represent individual columns within a table, containing a specific type of data for all rows, whereas rows (records) aggregate the data across those columns for one entity.
D. Tables: A table is a collection of rows and columns, not the same as a row itself. Rows are components of a table.
What does a CROSS JOIN do in a database system
-
Compares columns of two tables
-
Combines tables without comparing columns
-
Selects all rows from both tables
-
Selects only matching rows
Explanation
Correct Answer C. Selects all rows from both tables
Explanation
A CROSS JOIN produces the Cartesian product of two tables, selecting all possible combinations of rows from both tables. This join does not involve any condition or column comparison.
Why other options are wrong
A. Compares columns of two tables
A CROSS JOIN does not compare columns between tables. It simply combines all rows from both tables.
B. Combines tables without comparing columns
While a CROSS JOIN combines tables without comparing columns, its primary function is to produce a Cartesian product, not just to combine tables.
D. Selects only matching rows
A CROSS JOIN does not select only matching rows; instead, it selects all possible combinations of rows, regardless of matching criteria.
What does the SQL command 'CREATE TABLE Movie' do
-
Deletes the Movie table
-
Updates the data in the Movie table
-
Creates a table named Movie with specified columns and data types
-
Adds a new column to the Movie table
Explanation
Correct Answer C. Creates a table named Movie with specified columns and data types
Explanation
The CREATE TABLE command in SQL is used to create a new table in the database. The table is named as specified (e.g., Movie), and the command typically includes definitions for columns and their data types.
Why other options are wrong
A. Deletes the Movie table
The CREATE TABLE command does not delete a table. Deleting a table is done using the DROP TABLE command.
B. Updates the data in the Movie table
The CREATE TABLE command does not update data in a table. Updating data is done using the UPDATE command.
D. Adds a new column to the Movie table
Adds a new column to the Movie tableAdding a new column to an existing table is done using the ALTER TABLE command, not CREATE TABLE.
What happens when you define a primary key in a table
-
Primary
-
Composite
-
Unique
-
Key
Explanation
Correct Answer C. Unique
Explanation
When you define a primary key in a table, it ensures that all values in the specified column(s) are unique. This allows the primary key to uniquely identify each row in the table. Additionally, primary keys do not allow NULL values, further maintaining data integrity.
Why other options are wrong
A. Primary: While the term "primary" is part of the concept, it does not describe the effect of defining a primary key, which is ensuring uniqueness and integrity.
B. Composite: A composite key consists of multiple columns used together to create uniqueness, but this is not a requirement for every primary key.
D. Key: The term "key" is a general term that applies to various constraints, but it does not specify the effect of defining a primary key.
What is the difference between data and information in Business Intelligence
-
Data is raw value elements, while information is organized data with context.
-
Data is processed facts, while information is unprocessed.
-
Data is inferred, while information is calculated.
-
Data is collected, while information is stored.
Explanation
Correct Answer A. Data is raw value elements, while information is organized data with context.
Explanation
Data refers to unprocessed, raw elements that serve as inputs for analysis, while information is processed, organized, and structured data that provides meaning or context. In Business Intelligence, the distinction helps define how raw inputs transform into actionable insights.
Why other options are wrong
B. Data is not processed facts; that description applies to information. Information is derived after processing data.
C. Data is not inferred; inference involves analyzing data to draw conclusions, which is a step beyond raw data.
D. Data is not simply collected while information is stored. Both data and information can be stored, but their difference lies in processing and organization.
How to Order
Select Your Exam
Click on your desired exam to open its dedicated page with resources like practice questions, flashcards, and study guides.Choose what to focus on, Your selected exam is saved for quick access Once you log in.
Subscribe
Hit the Subscribe button on the platform. With your subscription, you will enjoy unlimited access to all practice questions and resources for a full 1-month period. After the month has elapsed, you can choose to resubscribe to continue benefiting from our comprehensive exam preparation tools and resources.
Pay and unlock the practice Questions
Once your payment is processed, you’ll immediately unlock access to all practice questions tailored to your selected exam for 1 month .
Frequently Asked Question
Our study pack includes 150+ expertly crafted exam questions with detailed rationales to help you fully understand key concepts.
The subscription is $30 per month, giving you full access to the study materials.
Yes! We guarantee a 100% pass rate when you use our materials effectively.
Simply visit ulosca.com, select the IITEC 2104 C175 study pack, and complete your subscription.
Yes! Our Q&A are designed to mirror real exam questions, ensuring you're well-prepared.
Absolutely! Every question comes with a clear and detailed rationale to deepen your understanding.
You will have unlimited access for the duration of your active subscription.
Yes! Whether you're new to data management or just need a refresher, our materials are structured to support all learners.